Project 1 of 1
Exploring the Ecosystem of DNS HTTPS Resource Records: An End-to-End Perspective
BibTex ↓Summary
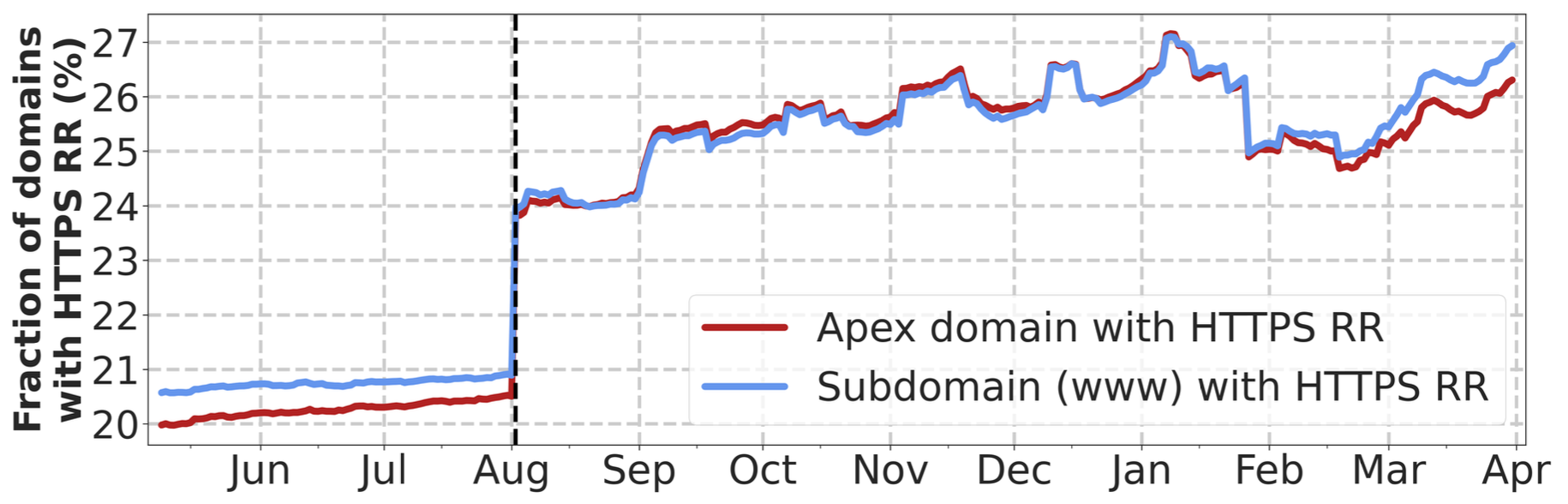
In this research, we investigated the adoption and management of DNS HTTPS records on both the server side (i.e., domains) and client side (i.e., web browsers). Specifically, we found that over 20% of Tranco’s top 1 million domains had DNS HTTPS records between May 2023 and March 2024, and major browsers utilize these records when establishing connections. Despite this growing adoption, our findings highlight challenges such as the proper maintenance of DNS HTTPS records and browser connection failures caused by misconfigurations.
Artifacts
We provide DNS HTTPS record datasets collected through daily scans of the Tranco Top 1 Million domains, along with code to reproduce the figures presented in our paper and scripts used for data collection.
Code
Code to reproduce figures and scripts used to collect DNS data for Tranco domains.
Reproducing Figures
Use parsed data in data/parsed/ or plotting data in data/plotting/. Open the Jupyter notebooks in notebooks/ to generate the figures.
Data Collection
Scripts for issuing DNS queries and testing TLS connection establishment behavior, including mismatched IP cases.
Dataset
Parsed DNS HTTPS measurements collected daily from our measurement server and released monthly.
Included Records
- HTTPS (and RRSIG if available)
- A, AAAA
- NS, SOA
Daily CSV Files
apex_https.csv,www_https.csvapex_flags.csv,www_flags.csv
Available Dataset Releases
File format:.tar.gz
| Date (YYYY-MM) | Download | Misc. |
|---|---|---|
| 2026-03 | Download | |
| 2026-02 | Download | |
| 2026-01 | Download | |
| 2025-12 | Download | |
| 2025-11 | Download | |
| 2025-10 | Download | |
| 2025-09 | Download | |
| 2025-08 | Download | |
| 2025-07 | Download | |
| 2025-06 | Download | |
| 2025-05 | Download | |
| 2025-04 | Download | |
| 2025-03 | Download | |
| 2025-02 | Download | |
| 2025-01 | Download | |
| 2024-12 | Download | |
| 2024-11 | Download | |
| 2024-10 | Download | |
| 2024-09 | Download | |
| 2024-08 | Download | |
| 2024-07 | Download | |
| 2024-06 | Download | |
| 2024-05 | Download | |
| 2024-04 | Download | |
| 2024-03 | Download | |
| 2024-02 | Download | |
| 2024-01 | Download | |
| 2023-12 | Download | |
| 2023-11 | Download | |
| 2023-10 | Download | |
| 2023-09 | Download | |
| 2023-08 | Download | |
| 2023-07 | Download | |
| 2023-06 | Download | |
| 2023-05 | Download |
Key Findings
DNS HTTPS Records Deployment
Over 20% of Tranco Top-1M domains publish DNS HTTPS records.
Cloudflare’s default DNS HTTPS config accounts for more than 70% of domains publishing HTTPS records.
ECH Deployment for DNS HTTPS–Supporting Domains
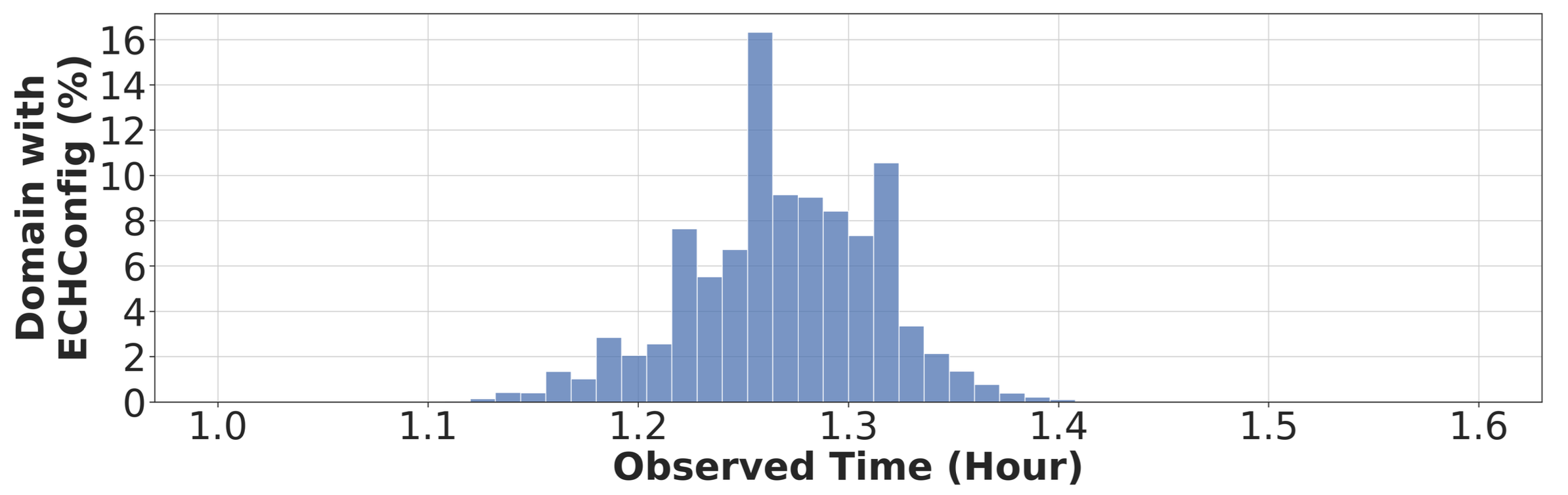
Before Oct 5, 2023 ~70% of apex domains with HTTPS records supported ECH (mostly Cloudflare). After that, ECH support dropped to 0% when Cloudflare disabled it.
Domains maintain ECH configs for ~1.26 hours on average, so frequent rotations risk key inconsistency.
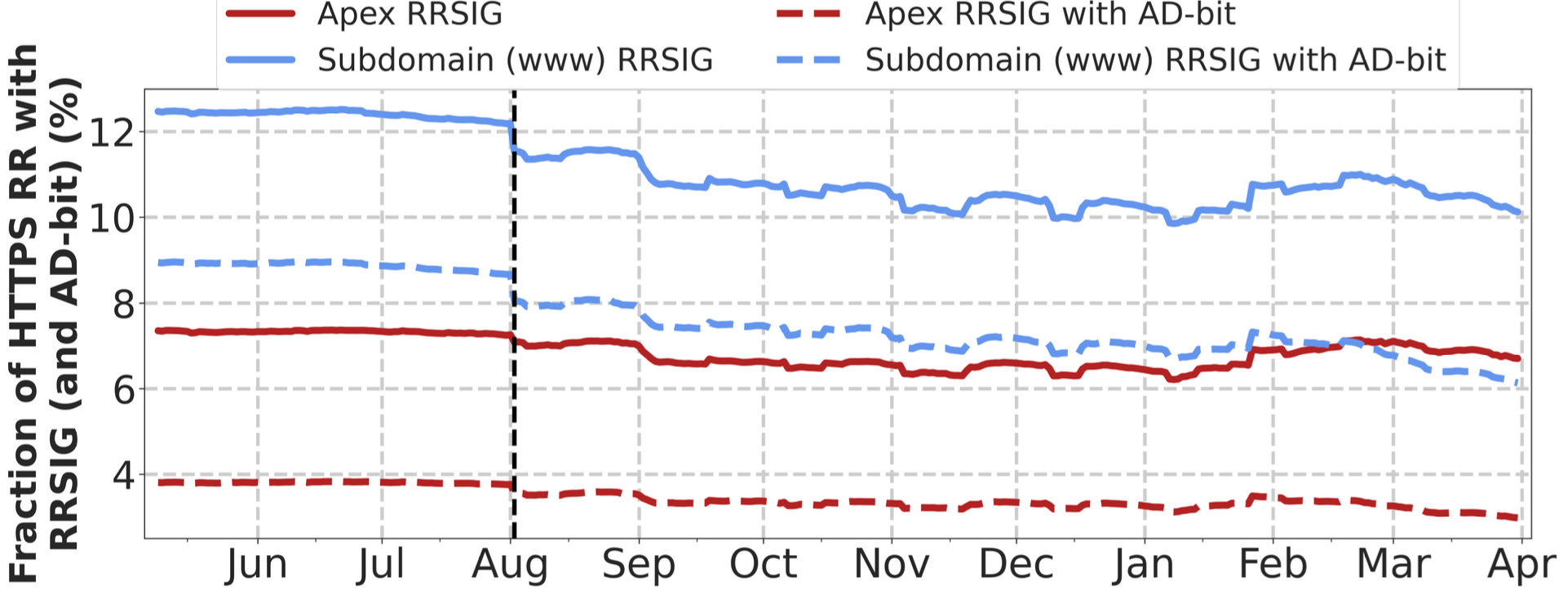
DNSSEC-Signed DNS HTTPS Records
The ratio of DNS HTTPS records protected by DNSSEC decreases over time.
Browser Support for DNS HTTPS Records
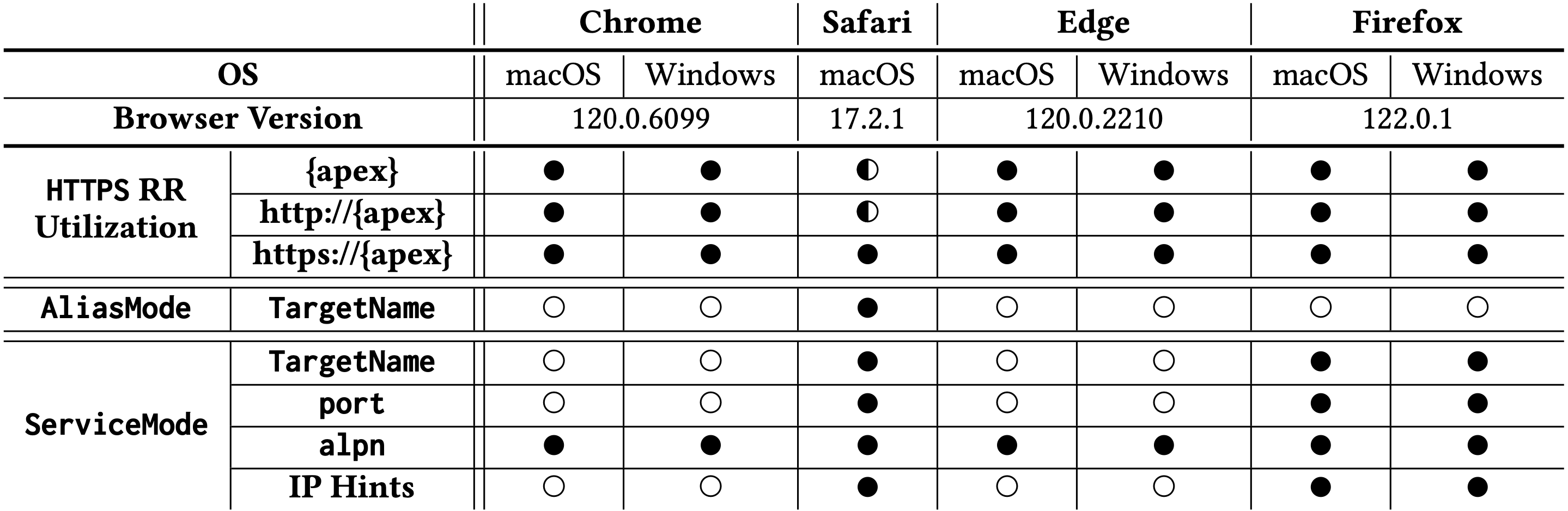
All major browsers query DNS HTTPS records but often fail to fully utilize the parameters.
Support varies by parameter; some are unsupported or partially implemented.
ECH Support in Browsers
Most browsers (except Safari) enable ECH by default, but critical functionality is missing; Split Mode connections fail.
This lack of support can disrupt servers deploying ECH configurations.
BibTex
@inproceedings{10.1145/3646547.3688410,
author = {Dong, Hongying and Zhang, Yizhe and Lee, Hyeonmin and Huque, Shumon and Sun, Yixin},
title = {Exploring the Ecosystem of DNS HTTPS Resource Records: An End-to-End Perspective},
booktitle = {Proceedings of the 2024 ACM on Internet Measurement Conference},
year = {2024},
series = {IMC '24},
pages = {423--440},
numpages = {18},
publisher = {Association for Computing Machinery},
address = {New York, NY, USA},
doi = {10.1145/3646547.3688410},
url = {https://doi.org/10.1145/3646547.3688410},
keywords = {dns, ech, encrypted clienthello, https resource record,
https rr, measurement}
}
Additional details are available. Expand sections below.